動的アプリケーションセキュリティテスト(DAST)
新しい環境にウェブアプリケーションをデプロイする場合、アプリケーションは新しいタイプの攻撃にさらされるかもしれません。例えば、アプリケーションサーバの誤った設定や、セキュリティ管理に関する誤った仮定は、ソースコードからは見え ないかもしれません。
動的アプリケーションセキュリティテスト(Dynamic Application Security Testing)(DAST) は、デプロイされた環境において、このような脆弱性についてアプリケーションを検査します。
概要については、動的アプリケーションセキュリティテスト(Dynamic Application Security Testing)(DAST) を参照してください。
GitLab DAST
GitLabは以下のDASTアナライザを提供しており、あなたがテストしているアプリケーションの種類によって一つ以上が役に立つかもしれません。
ウェブサイトをスキャンするには、以下のうちの一つを使います:
- 単純なHTMLを提供する従来のアプリケーションをスキャンする場合は、DASTプロキシベースアナライザを使用します。プロキシベースのアナライザは、自動またはオンデマンドで実行できます。
- DAST ブラウザベースアナライザ:JavaScript を多用するアプリケーションをスキャンします。これには、単一ページのWebアプリケーションが含まれます。
APIのスキャンには
- DAST API アナライザでウェブ API をスキャンします。GraphQL、REST、SOAP などの Web API テクノロジーに対応しています。
アナライザは、アプリケーションのセキュリティで説明したアーキテクチャパターンに従います。各アナライザはCIテンプレートを使用してパイプラインで設定でき、Dockerコンテナでスキャンを実行します。スキャンはDASTレポートのアーティファクトを出力し、GitLabはこのアーティファクトを使用して、ソースブランチとターゲットブランチでのスキャン結果の差異に基づいて発見された脆弱性を判断します。
利用を開始
前提条件
-
GitLab Runnerが利用可能で、Linux/amd64上で
dockerExecutor 。 - ターゲットアプリケーションのデプロイ。詳細については、デプロイオプションをお読みください。
-
dastステージをCI/CDパイプライン定義に追加します。これは、例えばデプロイステップの後に追加します:stages: - build - test - deploy - dast
推奨
- パイプラインが各実行で同じウェブサーバにデプロイされるように設定されている場合は注意してください。サーバーの更新中にDASTスキャンを実行すると、不正確で非決定的な結果につながります。
- 常にプルポリシーを使用して最新バージョンのアナライザを実行するように Runner を設定してください。
-
デフォルトでは、DASTはパイプライン内の以前のジョブによって定義されたすべてのアーティファクトをダウンロードします。DASTジョブが
environment_url.txt、テスト対象のURLや以前のジョブで作成されたその他のファイルの定義に依存していない場合は、アーティファクトをダウンロードしないことをお勧めします。アーティファクトのダウンロードを回避するには、アナライザ CI/CD ジョブを拡張して依存関係を指定しないようにします。たとえば、DAST プロキシベースのアナライザーの場合、.gitlab-ci.ymlファイルに以下を追加します:dast: dependencies: []
アナライザー設定
アナライザ固有の設定方法については、DAST プロキシベースアナライザ、DAST ブラウザベースアナライザ、またはDAST API アナライザを参照してください。
スキャン結果の表示
GitLab 13.1で導入されました。
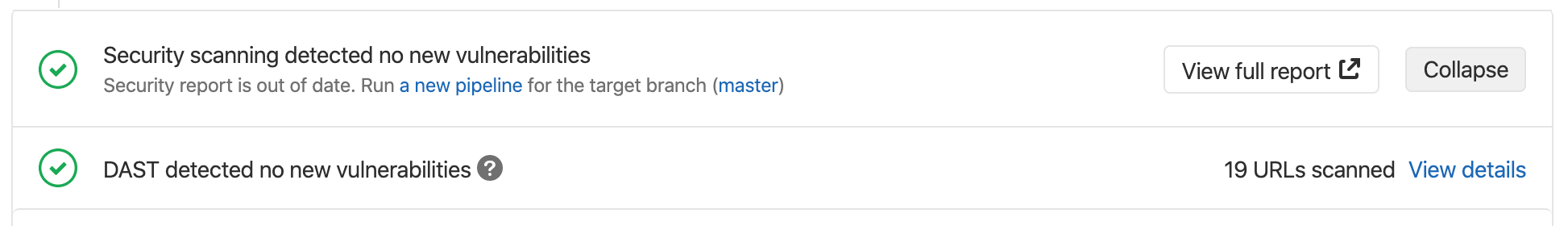
検出された脆弱性はマージリクエスト、パイプラインセキュリティタブ、脆弱性レポートに表示されます。
- 検出されたすべての脆弱性を表示するには、次のいずれかを実行します:
- プロジェクトで、「セキュリティとコンプライアンス」、「脆弱性レポート」の順に選択します。
- パイプラインから、[セキュリティ] タブを選択します。
- マージリクエストからセキュリティスキャンウィジェットに移動し、[フルレポート]タブを選択します。
-
DAST 脆弱性の説明を選択します。以下のフィールドは、根本的な原因の調査および修正を支援するために DAST アナライザが出力するフィールドの例です。アナライザによって出力されるフィールドは異なります。
項目 説明 説明 脆弱性の説明 証拠 脆弱性を検証するために発見されたデータの証拠。リクエストやレスポンスのスニペットであることが多く、脆弱性の検証に役立ちます。 識別子 脆弱性の識別子。 リンク集 検出された脆弱性の詳細へのリンクです。 方法 脆弱性の検出に使用される HTTP メソッド。 プロジェクト 脆弱性が検出された名前空間とプロジェクト。 リクエストヘッダー リクエストのヘッダー。 レスポンスヘッダ アプリケーションから受け取ったレスポンスのヘッダー。 応答ステータス アプリケーションから受信した応答ステータス。 スキャナの種類 脆弱性レポートの種類。 深刻度 脆弱性の深刻度。 解答 脆弱性に対する推奨される解決策の詳細。 URL 脆弱性が検出されたURL。
スキャンされた URL の一覧
DASTがスキャンを完了すると、マージリクエストページにスキャンされたURLの数が表示されます。スキャンされたURLのリストを含むウェブコンソール出力を表示するには、[詳細を表示]を選択します。
アプリケーションデプロイオプション
DASTでは、デプロイされたアプリケーションがスキャン可能である必要があります。
ターゲットアプリケーションの複雑さに応じて、DASTテンプレートのデプロイと設定方法にはいくつかの選択肢があります。DASTデモンストレーションプロジェクトでは、アプリケーションの例と設定を提供しています。
レビューアプリ
レビューアプリは、DASTターゲットアプリケーションをデプロイする最も複雑な方法です。このプロセスを支援するために、Google Kubernetes Engine(GKE) を使用してレビューアプリのデプロイを作成しました。このサンプルはReview Apps - GKEプロジェクトにあり、DAST 用の Review Apps の設定方法についてREADME.mdに詳細な説明があります。
Dockerサービス
アプリケーションでDockerコンテナを使用する場合、DASTでデプロイおよびスキャンするための別のオプションがあります。Dockerビルドジョブが完了し、イメージがコンテナレジストリに追加されると、そのイメージをサービスとして使用することができます。
.gitlab-ci.ymlでサービス定義を使用することで、DASTアナライザでサービスをスキャンすることができます。
ジョブにservices セクションを追加する場合、alias を使用して、サービスへのアクセスに使用できるホスト名を定義します。以下の例では、dast ジョブ定義のalias: yourapp 部分は、デプロイされたアプリケーションへの URL がホスト名としてyourapp を使用することを意味します (https://yourapp/)。
stages:
- build
- dast
include:
- template: DAST.gitlab-ci.yml
# Deploys the container to the GitLab container registry
deploy:
services:
- name: docker:dind
alias: dind
image: docker:20.10.16
stage: build
script:
- docker login -u gitlab-ci-token -p $CI_JOB_TOKEN $CI_REGISTRY
- docker pull $CI_REGISTRY_IMAGE:latest || true
- docker build --tag $CI_REGISTRY_IMAGE:$CI_COMMIT_SHA --tag $CI_REGISTRY_IMAGE:latest .
- docker push $CI_REGISTRY_IMAGE:$CI_COMMIT_SHA
- docker push $CI_REGISTRY_IMAGE:latest
dast:
services: # use services to link your app container to the dast job
- name: $CI_REGISTRY_IMAGE:$CI_COMMIT_SHA
alias: yourapp
variables:
DAST_WEBSITE: https://yourapp
DAST_FULL_SCAN_ENABLED: "true" # do a full scan
DAST_BROWSER_SCAN: "true" # use the browser-based GitLab DAST crawler
ほとんどのアプリケーションはデータベースやキャッシュサービスのような複数のサービスに依存します。デフォルトでは、サービスフィールドで定義されたサービスは互いに通信できません。サービス間の通信を許可するには、FF_NETWORK_PER_BUILD 機能フラグを有効にします。
variables:
FF_NETWORK_PER_BUILD: "true" # enable network per build so all services can communicate on the same network
services: # use services to link the container to the dast job
- name: mongo:latest
alias: mongo
- name: $CI_REGISTRY_IMAGE:$CI_COMMIT_SHA
alias: yourapp